Technology: Using trusted NTP in time based encryption
- Security Operations Team
- Jul 12, 2018
- 2 min read

One of the founding principal ideas in encryption is that it must take time to decrypt a message. In the early days of encryption it was believed that the security resulted from the number of years[1] required to break the encryption and recover the original data. As such time has always played an important key element in encryption methods and security.
So in this document we will talk about a method for ensuring the documents can withstand the time factor even with parallel computing and distributed computing making it easier to attack encryption methods.
Incorporating a different time element in encryption products
Since we know that the security of encryption relies on the amount of time required to recover the encrypted message or data, let's look at a method of securing data that uses verified time as part of the encryption process itself.
Some security encryption products on the market look to see if the encrypted message is "expired". The problem with this method is that in many cases these products look at the current time on the decryption machine. By leveraging a trusted "Network Time Protocol" server (NTP)[2], you can prevent the end user from changing the time within the application to trick the software into thinking that the message has not expired, allowing decryption on messages that may have already expired.
The method discussed is the use of a trusted NTP source that is required to ensure that a message is valid and has not expired in the decryption process. Utilizing a known trusted NTP server prevents time based attacks on the validity of the message which makes it harder to attack the actual encryption method.
It is recommended that only trusted NTP time servers are used when dealing with encryption. For more information see our previous discussions on Jigsaw Security's DataLock utility (see below). This software prevents time based attacks by incorporating secure NTP servers that are trusted and due to the fact that the encryption methods have never been made public so even if you can get around the time based issue, you would still have to figure out how the encryption actually works.
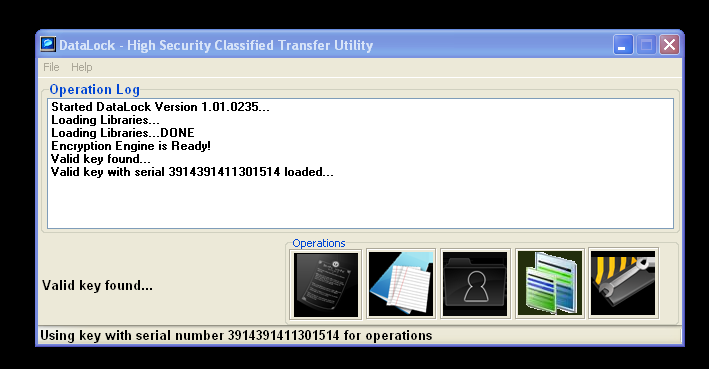
The DataLock program eliminates many of the issues with encryption products that are on the market. This software is what prevents data loss on classified and highly sensitive data.
References:
[1]: EFF DES cracker (Wikipedia): https://en.wikipedia.org/wiki/EFF_DES_cracker
[2]: NTP The Network Time Protocol: http://www.ntp.org/




Comments